Clear text unencrypted management protocols such as SNMPv1 or SNMPv2 are getting depreciated. I was a big fan of SNMPv2c for ages – it was easy to configure and worked well!
This is my SNMPv3 configuration example document for both Cisco and Juniper devices.
SNMPv3 Security Levels
We need to understand SNMPv3 security levels before we configure it. Following are the three supported security levels of SNMPv3.
(i) noAuthNoPriv – no auth, no data encryption crypto; no password required to set this up
(ii) authNoPriv – use SHA or MD5 password for auth, but no data encryption crypto; so, no password is required for data encryption
(iii) authPriv – use SHA or MD5 password for auth and use AES or DES password for data encryption crypto; this is the most secure option.
This document is based on “authPriv” with SHA for the password and AES for the data crypto. Let’s move on to the setup sections……
Setting up SNMPv3 on a Cisco IOS
The steps are simple and straightforward –
Step 1: Create an SNMPv3 view
Step 2: Create an SNMPv3 group that has access to the recently created view
Step 3: Create a user, and add it to the above group with an auth and data encryption passwords; we can add an ACL here as well to restrict the source.
! Following are the attributes used in this example - SNMPv3 UserName: test-snmp3-user SNMPv3 GroupName: test-snmp3-grp SNMPv3 AuthPassword: AUTH_PASSWD SNMPv3 CryptoPassword: CRYPTO_PASSWD SNMP ViewName: TESTSNMP3VIEW ! ! conf t ! ip access-list standard acl-snmp-ro remark SNMP read access permit 10.10.1.0 0.0.0.255 permit 10.11.10.0 0.0.0.255 ! !--SNMPv3 specific params-- snmp-server view TESTSNMP3VIEW iso included snmp-server group test-snmp3-grp v3 priv read TESTSNMP3VIEW snmp-server user test-snmp3-user test-snmp3-grp v3 auth sha AUTH_PASSWD priv aes 256 CRYPTO_PASSWD access acl-snmp-ro ! !--following are generic SNMP params-- snmp-server trap-source GigabitEthernet0 snmp-server source-interface informs GigabitEthernet0 snmp-server location "Equinix SY3" snmp-server contact nocsupport@company.com ! !--SNMP show commands-- show snmp show snmp user show snmp group !
Setting up SNMPv3 on a Juniper JUNOS
The following are the steps –
Step 1: Create an SNMP view that includes the OIDs
Step 2: Create an SNMPv3 user and a group with passwords for AUTH and CRYPTO
Step 3: Map the SNMPv3 user to the SNMPv3 group created for security access
Step 4: Set access for the group to the security context (default) with access to the view/OIDs
#
#The SNMPv3 params are same as the Cisco example
#
set snmp view TESTSNMP3VIEW oid .1 include
set snmp v3 usm local-engine user test-snmp3-user authentication-sha authentication-password AUTH_PASSWD
set snmp v3 usm local-engine user test-snmp3-grp privacy-aes128 privacy-password CRYPTO_PASSWD
set snmp v3 vacm security-to-group security-model usm security-name test-snmp3-user group test-snmp3-grp
set snmp v3 vacm access group test-snmp3-grp default-context-prefix security-model any security-level authentication read-view TESTSNMP3VIEW
set snmp v3 vacm access group test-snmp3-grp default-context-prefix security-model any security-level privacy read-view TESTSNMP3VIEW
#
#--following are generic SNMP syntaxes requires on JunOS--
set snmp description HOSTNAME-OF-DEVICE
set snmp location "Equinix SY3"
set snmp contact "nocsupport@company.com"
#
show snmp v3
#
Notes on the JUNOS syntax:
NOTE 1: After applying the above the command syntax, the "authentication-password" and "privacy-password" will get converted to -> "authentication-key" and "privacy-key"; in-case of COPY/PASTE of the syntax from a running Juniper devices - this needs to be fixed before applying. Also, enter password within "" punctuation marks.
NOTE 2: If the SNMP interface is in a "non-default" routing-instance, then you must configure SNMPv3 access to the "non-default" security context (i.e. routing-instance); example syntax following -
#
set snmp v3 vacm access group test-snmp3-grp context-prefix NAME-OF-CONTEXT-Routing-Instance security-model any security-level authentication read-view TESTSNMP3VIEW
set snmp v3 vacm access group test-snmp3-grp context-prefix NAME-OF-CONTEXT-Routing-Instance security-model any security-level privacy read-view TESTSNMP3VIEW
set snmp routing-instance-access
#
#
Testing the SNMPv3 Configs
Linux SNMPWALK can be used to test and verify the SNMPv3 configs above. Run the following command from Linux CLI.
snmpwalk -v3 -l authPriv -u test-snmp3-user -a SHA -A "AUTH_PASSWORD" -x AES -X "CRYPTO_PASSWORD" IP-Addr-of-Cisco-Juniper-Device
Let’s Add the Devices to a Monitoring System
In this example – I add the devices to LibreNMS monitoring system. We need the IP address of the devices and the SNMPv3 params that we applied during the above configs.
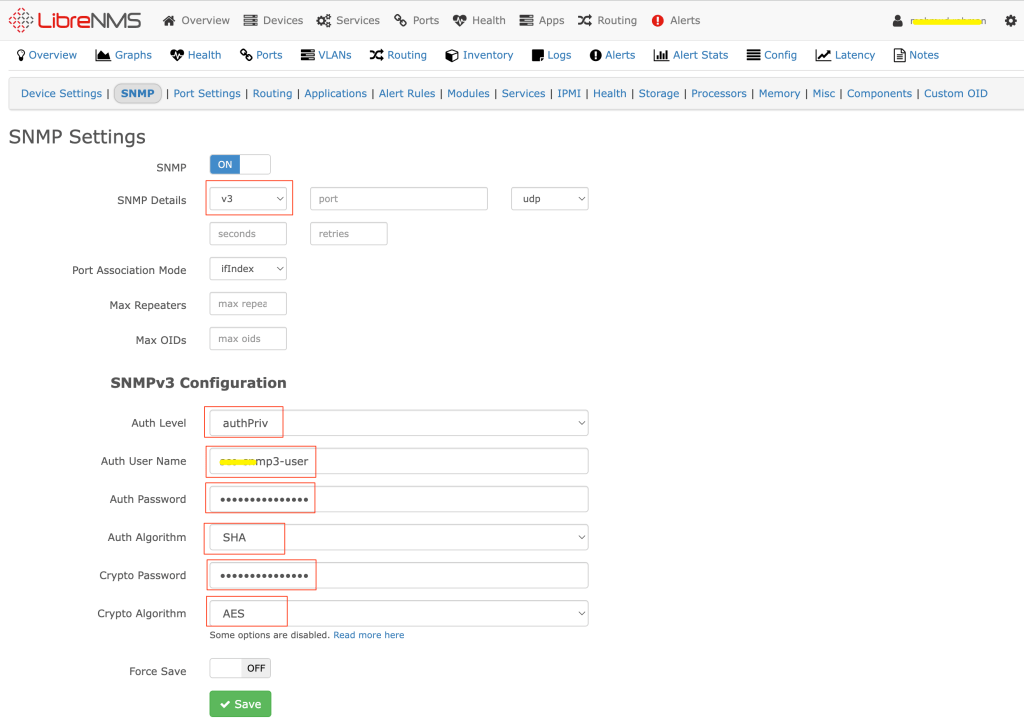
Now we should see device details (cpu, memory, traffic, interfaces, routing……) in the LibreNMS!
Make sure SNMP has been enabled on the device’s network interface and also there is no firewall rule that could block SNMP port UDP/161 access from the LibreNMS to the -> Cisco or Juniper devices.
