Recently I have implemented Windows Active Directory authentication for Splunk. My Windows AD DS is a mix of Windows 2008 and Windows 2012; Splunk version is 6.x.
Here is below the technical steps-
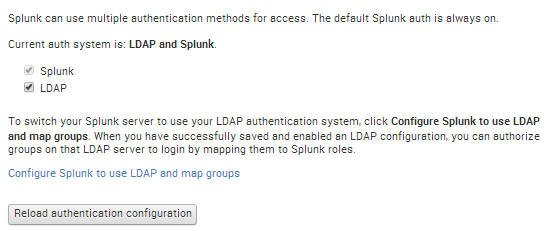
1. Login to Splunk using admin account. Go to “Settings > Access Controls > Authentication method”. You should be able to see the available authentication methods here. Select “LDAP” and click on “Configure Splunk to use LDAP and map groups”. Screenshot –
2. Click on the “New” button. On the new page – this is the main LDAP strategy configuration settings page. Following are the main AD items that you need to enter here –
a. LDAP connection settings – based on connection settings Splunk will talk to AD.
LDAP strategy name: just a name.
You can have multiple LDAP strategies such as – (i)strategy one for ready only access through an AD Group mapping to Splunk roles (user & power user), (ii)strategy two for full access through another AD Group mapping to other Splunk roles (Admin, Splunk-system-role) or similar.
Default Splunk roles are – admin, can_delete, power, splunk-system-role, user.
Port number: 389 (this is AD LDAP default)
Connection order: default
Bind DN: cn= AcctName Splunk,ou=yourSvcAcctOU,dc=yourDCName,dc=yourDCExtension
This is distinguished name of your Splunk account that you created in AD. It is recommended you should not use default AD administrator account or your own AD login here. You should create a dedicate account for Splunk – no AD administrative privilege required on this account.
Bind DN Password: enter the password of AD Splunk account
b. User Settings – Splunk will look for users in AD based on this
User base DN: dc=yourDCName,dc=yourDCextension
User base filter: leave this blank or you can enter specific AD search filter here
User name attribute: samaccountname
Real name attribute: displayname
Group mapping attribute: dn
Screenshot –
c. Group settings – Splunk will look for AD groups in AD based on this
Group base DN: cn=Group_Splunk_Access_Admins,ou=youGroupOUName,dc=yourDCName,dc=DCextension
This is the AD group that been created to grant access in Splunk.
Static member attribute: member
Screenshot-
d. Dynamic group settings – optional
e. Advanced settings – default is ok; however you can increase search request size limit.
Screenshot –
Click on the “Save”. If entered parameters are not correct – you won’t be able to save.
Now you should be able to see your LDAP strategy. Make sure it is enabled.
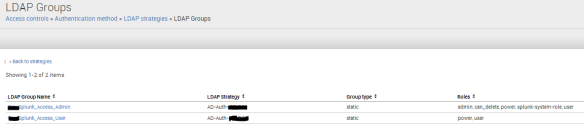
To see your AD group in Splunk, click on “Map groups”.
To map Splunk role(s) to an AD group – click on “Map groups > AD Group Name > available and selected roles”; screenshots –
Also you should be able to see AD users at “Settings > Access controls >Users”. Make sure AD users are member of the Splunk group that been created on AD.